Cloud Security
The architectural boundary between local development environments and global cloud infrastructures has dissolved, creating a lethal vector where a single compromised line of code can dismantle an entire enterprise ecosystem. The Cloud Supply Chain Attack represents a significant advancement in the cyber threat landscape. This review will explore
A single click on a file from a familiar messaging platform is now enough to trigger a sophisticated chain of events that strips Windows of its primary security layers. Recent investigations by Microsoft have uncovered a campaign that exploits the inherent trust of social communication to deploy malicious Visual Basic Script (VBS) files directly
Corporate boardrooms across the United States are currently recalibrating their financial compasses to navigate a massive wave of capital toward sophisticated autonomous systems. Average corporate spending has hit $207 million as organizations pivot toward AI agents as the new core of enterprise strategy. This transition from simple chatbots to
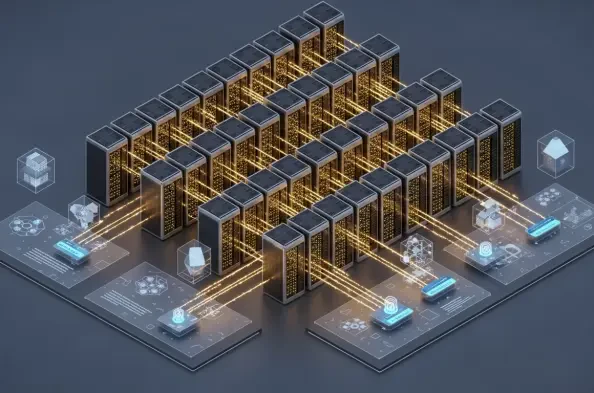
The architectural foundation of the modern digital world has shifted from simple data storage to a high-velocity engine that powers every interaction within the global economy. This transformation is not merely a quantitative increase in server racks or fiber optics but a fundamental qualitative change in how computing resources are orchestrated
Large enterprises are discovering that pouring billions into generative artificial intelligence without a robust cloud foundation is like trying to race a high-performance sports car through a dense, unpaved swamp. While the global appetite for automated decision-making and predictive analytics has reached a fever pitch, the underlying digital