Your trusted online source for Data Security and Management Information
 How Should CISOs Balance AI Hype With Security Reality?
How Should CISOs Balance AI Hype With Security Reality?Latest
Editorial
One breach can wipe out years of market momentum and put growth on hold. The average cost of a data breach in the U.S. has increased to over $10 million dollars , with containment often taking most of a year. That reality has pushed privacy from a back-office concern to a board-level discipline that directly affects revenue, valuations, and deal velocity. Privacy and security are now core business functions, and Data Protection Officers (DPOs) who treat them as such are the ones building programs that hold up under regulatory scrutiny, survive incidents, and earn the trust that accelerates growth. This article covers how DPOs can build and operate data protection programs that reduce regulatory exposure, protect organizational trust, and demonstrate measurable value to the business. Privacy Is a Business Asset, and DPOs are the Architects Data or Information privacy is the disciplined
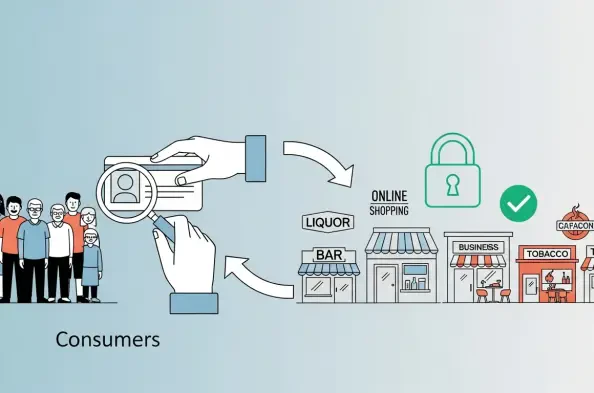
For many enterprises, age checks have moved from being a nice-to-have element in the legal department for compliance to a mandatory item on the product roadmap. More than ever, they influence conversion, brand safety, and the cost of doing business. Decision-makers must treat them as part of the business, with clear service-level agreements, rather than as one-off compliance tasks. And the companies that will win in 2026 are those delivering age assurance that is fast, private, and portable across all relevant business regions without eroding trust or creating risks. What are age checks? Age verification confirms that a user meets a minimum threshold, but the real question is how to verify this attribute with minimal friction and limited data exposure. Legacy flows that require credit card details or full identity documents increase abandonment and create new attack surfaces. A modern
Popular
The sheer scale of modern healthcare infrastructure has created a paradox where the very systems designed to provide seamless care now represent some of the most lucrative targets for global cybercriminal syndicates. In May 2026, this vulnerability
The digital security landscape has transformed into a complex battlefield where the assumption of absolute safety is increasingly viewed as a dangerous fallacy by both security professionals and casual users alike. For the better part of the current
The sudden revelation of the YellowKey zero-day vulnerability has sent shockwaves through the cybersecurity community, exposing a critical flaw in the way modern Windows operating systems handle encrypted volumes during recovery operations. Unlike many recent software vulnerabilities that require complex remote execution chains, this specific
The increasing frequency and sophistication of ransomware attacks targeting healthcare infrastructure have forced medical institutions to reconsider their reliance on traditional perimeter-based security models that often fail under pressure. This shift is characterized by a transition from reactive defense strategies to proactive operational
Mobile subscribers across the Nigerian telecommunications landscape have frequently expressed frustration regarding the mysterious speed at which their data allowances seem to evaporate during routine internet browsing sessions. In direct response to these pervasive concerns, a comprehensive digital portal was unveiled to provide users with an
 AI and Automation Redefine Endpoint Security in 2026
AI and Automation Redefine Endpoint Security in 2026 Is Your Organization Ready for 12-Hour Cyber Patching?
Is Your Organization Ready for 12-Hour Cyber Patching? Is Your Clean Pentest Report a False Sense of Security?
Is Your Clean Pentest Report a False Sense of Security? Lean AI Transformation – Review
Lean AI Transformation – Review